Microsoft Viva takes over the functionality of the My Analytics and Workplace Analytics features step by step. And there is also a lot going on in the backend. The MeetingInsights and ItemInsights endpoints have been customizable for some time and now the PeopleInsights endpoint can also be configured. This affects the following areas:
- Profile Cards
- User Profile in Delve
- Listing relevant people / working with overview
Customize Insights
In general, the ItemInsights as well as the PeopleInsights can now be customized. The respective endpoint can be completely disabled or enabled / disabled for an Azure-AD Group. The third category, MeetingInsights, can only be globally enabled or disabled.
Details on ItemInsights and MeetingInsights: Customizing item insights privacy in Microsoft Graph
Customize PeopleInsights
PeopleInsights show relationships between people. This evaluates public signals such as joint Microsoft 365 Groups / Teams or shared Exchange distribution lists. This data is displayed in Delve and the profile cards in Microsoft 365 and can be queried via the API:
By default, this feature is enabled in a Microsoft 365 tenant. The following options are available for customization:
- Disable PeopleInsights for all users:
PATCH, beta:{"isEnabledInOrganization": false}
- Disable PeopleInsights for an Azure AD Group by additionally using the disabledForGroup paramter:
PATCH, beta:{"isEnabledInOrganization": false,"disabledForGroup": "f742839d-2321479-4de9-9616-e61877675c88c"}
To do this, for example, with Microsoft Graph Explorer, the following steps are performed:
- Open Graph Explorer and log in: https://developer.microsoft.com/en-us/graph/graph-explorer
- GET, beta: https://graph.microsoft.com/beta/organization returns the OrganizationId that is needed in the next step:
- Get the current settings:
GET, beta: https://graph.microsoft.com/beta/organization/{organizationId}/settings/peopleInsights
- Customize the settings as needed:
PATCH, beta:{"isEnabledInOrganization": false,"disabledForGroup": "f953948d-3423-4ac7-9616-d6187975c00c"}
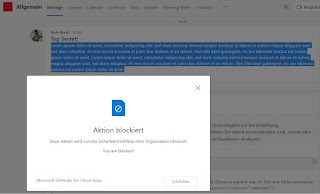
Effect: No more users are displayed in the "works with" section:
Important:
- The settings for PeopleInsights are currently only available in BETA.
- The update process does not check if an Azure AD Group exists. If the Group does not exist, no changes will be made for any user.
- It can take up to 24 hours for insightsSettings adjustments to take effect, or longer in the BETA version.